Developing A Cloud-Based Security Culture in Modern Businesses
It’s no exaggeration to say that cybersecurity is now an integral part of every modern corporate strategy. Every organization should have at least basic security protections: a minimum standard of policies and procedures for keeping their operations safe, from the threat of cyberattacks to adhering to government-regulated compliance standards to password management.
It will help if you secure your clients’ businesses as well as your own against security threats. You must, though, remain focused on your bottom line; while it’s pleasant to think of yourself as your clients’ guardian, you must still manage a business.

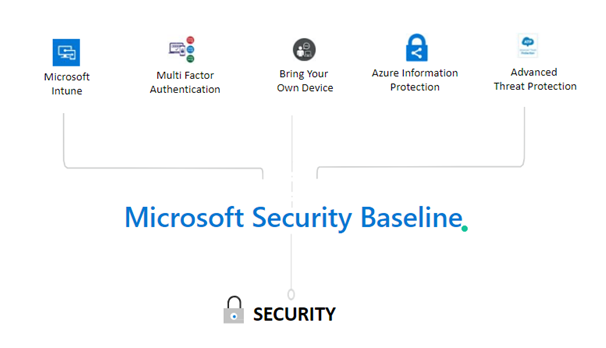
This is when Microsoft Security Baseline Services come into play. To ensure that your security solution is helpful for clients, there are a few crucial areas to keep an eye on. Covering these major areas can also be thought of as a basic set of safeguards to protect your organization and your clients from malicious assaults and unintentional security breaches.
What to do if your company has been hacked! Have you thought about this?
- How much will it cost you to communicate to all your customers? Will they stay with you after this?
- How long will it take to figure out the breach and resolve it without the right tools?
- How much time and distraction will this cost your company?
- How much time and distraction will this cost your company?
Everything you need to know about Microsoft Security Baseline
There are a few distinct views of what constitutes a Security baseline. A “security baseline,” according to the National Institute of Standards and Technology (NIST), is “the collection of basic security measures prescribed for a low-impact, moderate-impact, or high-impact information system.” A set of information security controls developed through information security strategic planning efforts to handle one or more specific security categorizations.”
To cut through the terminology, consider baseline security as the essential minimum that a company needs to adequately defend itself from vulnerabilities and attacks while remaining productive and efficient. This includes the necessary minimum of security solutions that we can provide to deploy and maintain that protection.
Unfortunately for all of us, cybersecurity is not a one-size-fits-all, one-and-done solution. There isn’t a magic cybersecurity button we can click to instantly prevent and deflect all of the harmful behaviors that threaten our company’s data. Vigilance, awareness, training, and monitoring are all necessary components of good cybersecurity. Regardless of how little our company is or how uninteresting we believe we are as prospective targets, we all require it.
On the plus side, organizing a consistent set of policies, procedures, and solutions to create robust baseline security. Security assessments, security for key productivity suites such as Microsoft 365, endpoint protection, email security, and backup and disaster recovery are all areas to concentrate on.
Security assessments
You’re only as good as the data you have, and cybersecurity assessments are one method you may obtain helpful information about your surroundings and current security procedures. Conducting thorough, regular cybersecurity assessments can assist in determining what security measures clients have implemented (if any) and where resources should be invested to strengthen defenses.
Microsoft Office 365 security
Stay protected with Microsoft Intune
Microsoft Intune is cloud-based mobile device management (MDM) and mobile application management service (MAM). You have complete control over how mobile phones, tablets, and laptops are used in your company. To control applications, you can also set up custom policies. You can, for example, block emails from being sent to persons outside your company. People in your business can also use their devices for education or work using Intune. Intune helps ensure that your organization’s data is protected on personal devices by isolating organization data from personal data.
- You have complete control over how your business’s technology is used.
- To control applications, set up specified policies.
- Being safe and having the best possible user experience.
- With Intune, you can choose to be entirely cloud-based
- Create rules and customize settings on personal and corporate devices.
- Authenticate and deploy apps on both on-premises and mobile devices.
- Control how people access and distribute information to protect your company’s data.
- Make sure your devices and apps meet your security needs.
- Protect data whether or whether the device is enrolled.

BYOD in the Workplace
Bring your device (BYOD) is a phrase that means “bring your device.” It’s an IT policy that permits (and sometimes promotes) employees to use personal mobile devices like smartphones, tablets, and laptops to access company data and systems. BYOD policies are crucial because they allow businesses to achieve a balance between increased productivity and risk management.
- Allow employees to use their laptops, smartphones, tablets, and other devices at work.
- Unprotected and unmanaged devices should be monitored.
- Capabilities for Data Encryption
- Multi-factor authentication should be enabled.
- Ex-employees should be protected against data theft.
Defend Office 365 against sophisticated threats with Advanced Threat Protection
Advanced threat protection (ATP) is a security technology category that safeguards sensitive data against sophisticated malware or hacking-based attacks. Advanced threat protection software and managed services are both available. Endpoint agents, network devices, email gateways, malware protection systems, and a centralized management dashboard to correlate warnings and control defenses are all standard components of ATP solutions.
- Anti-phishing software scans
- ATP Safe Links provides real-time scanning to protect against harmful links in email and Teams.
- Experiential learning aids in the identification, prioritization, and investigation of threats.
- Capabilities for large-scale incident response and automation.
- Reports and insights in real-time.
- Use Safe attachment policies to ensure that the files you receive aren’t harmful.
- Examine the URLs and links.
With Azure Information Protection, you can manage and help safeguard email, documents, and sensitive data.

Set up policies to categorize, label, and safeguard data according to its sensitivity. With Azure Information Protection, classification is entirely automated, driven by users, or based on recommendations.
- Create policies that categorize, label, and safeguard data according to its sensitivity.
- Classify emails and documents based on pre-defined rules.
- Keep track of what’s going on with shared data and, if necessary, cancel access.
- Share data with coworkers, customers, and partners in a secure manner.
- Protect company’s confidential files with Rights Management
- Encrypt the files to a specific set of recipients.
Computer Solutions East is a Microsoft Gold Certified Partner who follows the best IT cyber security baseline practices to help organizations limit their data vulnerability and prevent persistent attacks. Begin by establishing a streamlined Baseline basis for enterprises to use Microsoft 365 with dual-level security settings. Call us now to know more


