
Cloud Computing for Small Businesses
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

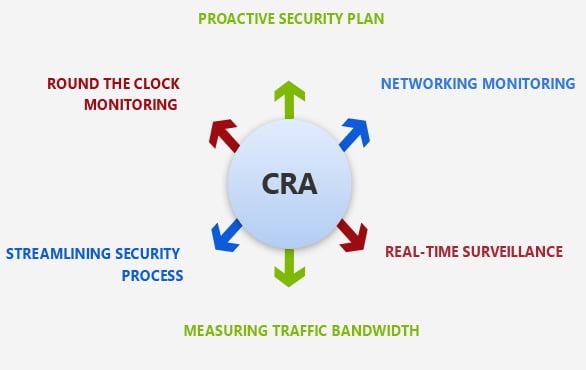
A security model that can protect your business and enable growth.





We possess a team of network admins who ensure network security by remaining proactive. The first step is to check the network performance on various applications, connections, devices, and traffics. The next step involves structured networking monitoring, phase-wise, based on various departments and business requirements. Our team looks for the suspected traffic as the network surveillance gets top priority. It is followed by the next phase of efficient network mapping where the inter-mapper will work as a vendor-agnostic program to run checks periodically. We then take the step to monitor the bandwidth traffic on specific devices like solid network security monitoring tools and monitoring traffic for other devices. Later, we implement efficient and lean monitoring methods to abstract real-time networking information and generate statistical data from the existing one. The next step is to ensure that network processes are streamlined as planned during the deployment. Our network security team will then ensure implementing security tools at the right endpoints. For the next step, our network monitoring team will come into action and take a close look at the efficiency issues in the infrastructure.

Providing you with a team of certified network experts to monitor threat, real-time.

We keep a long of network breaches to ensure network safety and tools retention over time.

The compliance report help teams to work on legal issues that requires sorting network issues.

We implement intelligent software and stay vigilant to detect the threat and counter it.

We ensure managed archiving all the network to support audits.

Dedicated team ensure timely updating the firewall for network security.

You will have access to certified network security analysts 24/7.
Our core network security team is an expert in monitoring the real threats in your network environment by providing context and taking actionable steps to eliminate them. Choosing CSE means enabling data analytics and full packet capture technology for your network that assures availing threat monitoring – 24×7. We are also experienced in providing you with the real-time investigation alerts and reports on file analysis that work as a testament to network monitoring activities. Our range of tasks for such security includes classification of data source and groupings, platform incident management, enabling native reporting, periodic health checks, problem management, and release management.
Our cloud solutions help the global enterprise achieve business goals.

We work to identify the clients IT problem and offer the best solution. Time and again,we face a situation that demands agility and the right set of talent that can solve technology issues.
Learn More
Not all projects are about innovation. Some are those that add a feather in our cap no matter what we deliver and how. It was typically a government project that involved a lot of roadblocks right.
Learn More
Being an expert IT solutions partner in the US and worldwide, we are committed to delivering results that drive business growth. Our team recently worked with Neil Hoosier & Associates to resolve.
Learn More
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

Technology has been transforming businesses ever since the invention of the wheel. However, in recent years, the business landscape has …
Continue reading “Azure Secrets: The Key to Secure & Automated Cloud Workflows”

Effective communication is important for the success of any team. But with so many options, choosing the right platform can …
Continue reading “Choosing the Right Collaboration Tool: Microsoft Teams vs. Slack”

Cloud computing services allow businesses to undergo digital transformation, which can enhance efficiency and reduce expenses. Choosing the most suitable …
Continue reading “A Guide to Managed Cloud Computing Services”