
Cloud Computing for Small Businesses
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

A reliable cloud security testing in the USA for an enterprise to identify critical vulnerabilities and save cloud assets from threat exposures.





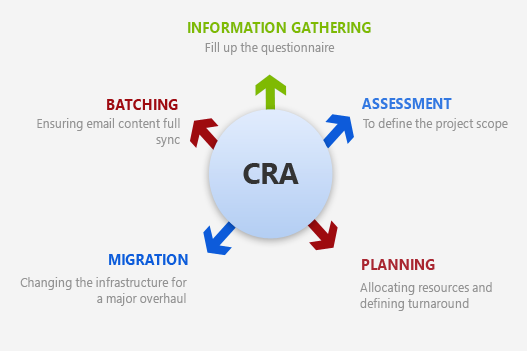
CSE’s cloud security testing process is highly customizable, considering your cloud requirements and a long-term cloud strategy. All begins with the information collected in which the experts at CSE conduct thorough recognition of the program, which includes its architecture, functions, and security controls. Here, our dedicated cloud security testers also avail the necessary inputs from the development team to determine the scope of cloud penetration testing. Based on the previous step’s collected data, the CSE experts develop a systematic approach that imitates real-time attacks and checks for any existing vulnerabilities.
We plan an attack to reduce the impact, whether on stupid surroundings or in the lowest network operation (most low traffic). At this point, we run vulnerability scanners to explore the potential platform, API, technology system, etc., as a way of safeguarding the cloud security penetration testing at all levels. Such penetration techniques are useful for enterprises to scale up or limit their cloud infrastructure whenever required.
The next step involves conducting an in-depth penetration test where the cloud testing experts at CSE utilize the application to determine its protection. To achieve a high level of penetration, the technical staff are equipped with custom scripts, open-source codes, and in-house tools for azure cloud penetration testing. The next phase will then have a testing team produce brief and concise reports of the vulnerabilities found and discuss the exposure’s essence, its effects, threat level, and a vulnerability elimination recommendation.
The outcome at each stage of cloud penetration testing is thoroughly measured to ensure no loopholes within the cloud architecture. Cloud testing reports often follow such reviews by looping in the customer development team to identify errors and measure its impact. At both ends, teams can run the tests and measure vulnerability testing efficiency while conducting reviews on eliminating possible bugs without affecting the hardware devices.

Fully assess the protection of a device by simulating malicious user behavior.

Our cloud security experts evaluate and consult cloud migration initiatives to ensure that threats are detected.

Ensuring compliance of IT facilities, processes and systems with global compulsory standards and regulations.

Helping businesses identify the level of knowledge among employees of social engineering risks.

Enabling white box testing to examine the application's source code and find possible security bugs and defects.

Our Cybersecurity experts will help your company adjust, fill essential loopholes, and win more clients.

Active guidance from the start of the contract to the end of the remediation by a trusted partner
Our security testing experts will provide IT audit services and penetration testing services to your company and offer daily recommendations to protect your data. You can trust us with our cloud security penetration testing if your organization needs to cloud security testing for data and software. It enables businesses to use web application penetration tests’ true power, which analyzes overall protection and potential risks of web applications, including code bugs, authentication or broken permission, and external vulnerabilities.
Hiring a dedicated cloud security testing team pays off by providing you with a robust security environment. Such a team will ensure securing your critical business data from the existing cloud vulnerabilities and thereby save your brand reputation in the longer run. Experts at CSE are provided with the right tools, experience, and knowledge to refine cloud processes and implement stronger security protocols. This involves providing a dedicated team of cybersecurity experts who can provide constant monitoring across multiple cloud devices.
Our cloud solutions help the global enterprise achieve business goals.

We work to identify the clients IT problem and offer the best solution. Time and again,we face a situation that demands agility and the right set of talent that can solve technology issues.
Learn More
Not all projects are about innovation. Some are those that add a feather in our cap no matter what we deliver and how. It was typically a government project that involved a lot of roadblocks right.
Learn More
Being an expert IT solutions partner in the US and worldwide, we are committed to delivering results that drive business growth. Our team recently worked with Neil Hoosier & Associates to resolve.
Learn More
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

Technology has been transforming businesses ever since the invention of the wheel. However, in recent years, the business landscape has …
Continue reading “Azure Secrets: The Key to Secure & Automated Cloud Workflows”

Effective communication is important for the success of any team. But with so many options, choosing the right platform can …
Continue reading “Choosing the Right Collaboration Tool: Microsoft Teams vs. Slack”

Cloud computing services allow businesses to undergo digital transformation, which can enhance efficiency and reduce expenses. Choosing the most suitable …
Continue reading “A Guide to Managed Cloud Computing Services”