Providing best integrating threat management process customized by CSE team.
More than detecting and reacting to ongoing attacks against the company is needed to manage cyber threats effectively. It includes negating the possible harm and expense of these attacks; effective security measures and resources capable of detecting and preventing them are needed.
An organization’s network security policy should include a threat management framework, a mechanism that allows a security team to handle possible cyber-attacks against the entire company from a single location. It enables technical safeguards to react to possible cyberattacks and other events more rapidly and efficiently through unifying threat detection across the entire enterprise.
The threat identification and the management of threats are frequently viewed as separate activities, although the same staff supervises all. Current evidence suggests that, when coupled, such characteristics will associate with an increased risk of aggression. The study further demonstrates the integration of hazard evaluation and management systems in a mutual support cycle. Hear how the selection and use of the tools and methodologies tested by peers will direct the threat assessment process through investigation, evaluation, and management phases.
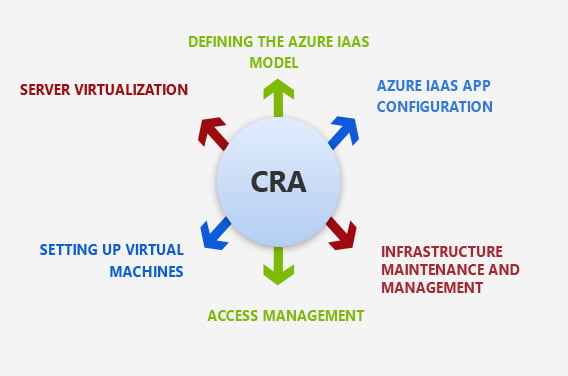
Integrated Threat Management (ITM) from CSE makes cybersecurity teams more effective and intelligent. The solution architecture and methodology incorporate identification, triages, improvisation, interpreted control of incidents, and a streamlined experience investigation to minimize the mean response time (MTTR) for each incident. The system learns from the interactions and research of analysts to help cybersecurity teams take the best moves.
Wipro is at the forefront of this evolution, exploiting unique cyber investments through our projects supplying consumers with the most up-to-date solutions and managed services. By integrating cybersecurity solutions and adding cyber symmetry, we resolve the problems faced by CISOs and Cyber Operations teams.
Consequently, suppliers of information technology solutions must keep pace with the proliferation of endpoint risks to protect against networked attacks. What began with DOS viruses a decade ago has progressed to macro viruses, spam, spam, and mixed threats that combine viruses, worms, Trojans, spyware, botnets, null-day threats, port attacks, fully released disk encryption, phishing, and spam.
Crossing today’s threatening world, stubborn and financially driven criminals use endpoint software vulnerabilities. Very many of the exploits are subtle enough to prevent conventional defense strategies from being detected. Too many small and big targeted organizations all suffer from business-critical services disruptions and learn too late that their data have been hacked or stolen.