
Cloud Computing for Small Businesses
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

Protect all of Office 365 against advanced threats like business email compromise and credential phishing.





Protection powered by identity is at the root of cloud safety solutions from Microsoft, such as Azure AD, Azure, and Intune. An additional layer of security in the ever-evolving threat environment offers Advanced Threat Analytics for businesses that track attacks against their existing local authentications. The days are gone when conventional safety protections such as firewalls and basic anti-virus applications have been relied upon. Advanced Monitoring for Threats is included here. Unusual, bizarre behaviors can be detected utilizing intrusion sensing and prevention systems (IDPS) using behavioral analysis and machine learning. Thus, steps can be placed in place to avoid such an attack. We will also enable you to evaluate safe links that are close to safe links, but to search for harmful links via email and office documents. Initially, Office 365 Share Online Protection uses signature malware protection, Internet Protocol (IP), anti-spam, and malware filters. Our experts assist you in the automated spoof detection with Office 365 Advanced Threat Security. If you spoof yours or the email from some other agency, you must know. In the battle against spear-phishing attacks, this defense is especially important since many businesses are infiltrated with this form.
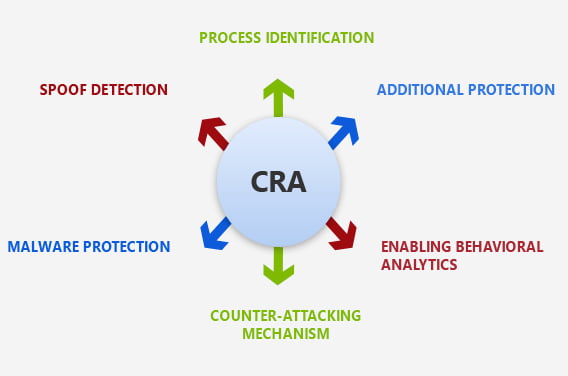

We equip the O365 ATP system to recognize connections between end-users, equipment, and networks, and detect changes in these regular patters.

Our experts will search for pattern anomalies compared to previous applications from that domain.

A checklist of safe dispatch and a history of previous dispatches from that domain is also created.

CSE provides the IT teams in your enterprise with a clear identification of all incoming zero-day attacks where malware previously is unknown.

Make use of our Microsoft collaboration to directly support Microsoft.

A robust filtering stack prevents a wide variety of volume-based and targeted attacks including business email compromise, credential phishing, ransomware, and advanced malware.

Offering you a world-class environment, which enhances company efficiency.
We are the facilitators who believe in the potential of technology resources that can stand up to the influence of the industry for small and medium enterprises. With a team of experienced executives, CSE has comprehensive know-how to handle even the more complicated Office 365 projects. Work with our dedicated Office 365 ATP team to manage specific tasks requiring the right guidance for your request. Join long-term commitment, as we have Office 365 Advance Threat Protection full-time professional support to ensure the security of your office data 365.
Our cloud solutions help the global enterprise achieve business goals.

We work to identify the clients IT problem and offer the best solution. Time and again,we face a situation that demands agility and the right set of talent that can solve technology issues.
Learn More
Not all projects are about innovation. Some are those that add a feather in our cap no matter what we deliver and how. It was typically a government project that involved a lot of roadblocks right.
Learn More
Being an expert IT solutions partner in the US and worldwide, we are committed to delivering results that drive business growth. Our team recently worked with Neil Hoosier & Associates to resolve.
Learn More
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

Technology has been transforming businesses ever since the invention of the wheel. However, in recent years, the business landscape has …
Continue reading “Azure Secrets: The Key to Secure & Automated Cloud Workflows”

Effective communication is important for the success of any team. But with so many options, choosing the right platform can …
Continue reading “Choosing the Right Collaboration Tool: Microsoft Teams vs. Slack”

Cloud computing services allow businesses to undergo digital transformation, which can enhance efficiency and reduce expenses. Choosing the most suitable …
Continue reading “A Guide to Managed Cloud Computing Services”