
Cloud Computing for Small Businesses
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

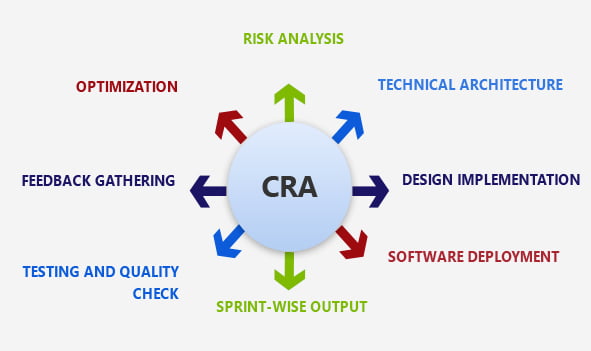
We are responsible for providing security during the development stages of software systems, networks and data centers.





Information security reviews assess the maturity of the ISP and recognize vulnerabilities, limitations, and opportunities for development. The CISO provides you with wide expertise needed in response to the accidents and enforcement, as well as the current information security vulnerabilities and in carrying out actionable measures to mitigate them. The CISO provides a broad range of expertise. The next step is to expose attackers as they pass across layers: Attackers can use any layer of your stack to reach it, create footprints, and pass it laterally. Visibility of the full stack allows us to notice the step to interrupt the attack — before it is too late. You are protecting more of your expanded attack area by using commercial and open-source platforms such as Joomla, WordPress, Magento, PHP, and ASP.NET. You are inheriting vulnerabilities In order to understand this weakness, vulnerabilities, and attack behavior, we invest in proprietary analysis and threatened intelligence. And then sophisticated network attacks are identified by experts. When short development cycles leave little time to implement and test safe coding and configuration, you add your own vulnerabilities like OWASP Top 10. Our experts are given an industry-leading instrument collection for the detection of stubborn attacks, including the SQL Injection, with advanced analytics of detection like machine learnings and anomaly sensing.

Curated information security specialists actively track, triage and escalate the threats that are most important.
Our experts in cybersecurity simulate attacks to check whether they can help deter, track and fix.

Our experts are researching, implementing and constantly developing logic identification and blocking, such as signatures, rules, and enforcement.

Build and train algorithms with data scientists to identify advanced multi-stage threats.

We watch for threats and identifying the new developments in how adversaries work.

Our specialist comes with experience collaborating with companies with diverse partners

CSE have accredited information security training programs as part of the Organizations security audit.
To defend the organization, we offer end-to-end training, security, and monitoring services. Based on your current maturity level, we advise on your cybersecurity plan to help you identify your perimeter, priorities, and procedures for protection. With our cybersecurity solutions, we secure your infrastructure and track your network to detect and respond to cyber- in advance. Secure the digital organization from cyber-attacks and internal malicious activity with end-to-end advice, protection and monitoring services.
Our cloud solutions help the global enterprise achieve business goals.

We work to identify the clients IT problem and offer the best solution. Time and again,we face a situation that demands agility and the right set of talent that can solve technology issues.
Learn More
Not all projects are about innovation. Some are those that add a feather in our cap no matter what we deliver and how. It was typically a government project that involved a lot of roadblocks right.
Learn More
Being an expert IT solutions partner in the US and worldwide, we are committed to delivering results that drive business growth. Our team recently worked with Neil Hoosier & Associates to resolve.
Learn More
Cloud computing is a modern approach to managing and processing data through remote servers hosted on the internet, which provides …

Technology has been transforming businesses ever since the invention of the wheel. However, in recent years, the business landscape has …
Continue reading “Azure Secrets: The Key to Secure & Automated Cloud Workflows”

Effective communication is important for the success of any team. But with so many options, choosing the right platform can …
Continue reading “Choosing the Right Collaboration Tool: Microsoft Teams vs. Slack”

Cloud computing services allow businesses to undergo digital transformation, which can enhance efficiency and reduce expenses. Choosing the most suitable …
Continue reading “A Guide to Managed Cloud Computing Services”